Whistleblowing – Infrastructure and Application Security
Reports and whistleblowers’ safety
- Asymmetric cryptography on textual contents and attachments. Encryption does not require specific actions by the anti-corruption supervisor, the whistleblower, or any interventions by system administrators. The cryptographic system guarantees that messages and their attachments can only be read by the sender and recipient through the pairing of two public and private cryptographic keys.
- Transmission of the digital fingerprint of the message (hash) to the whistleblower e-mail, ensuring the unchangeability of the reports.
- Login with smart card.
- Access is regulated under the privacy policy (password complexity and change);
- Two-factor authentication and login through biometric credentials (fingerprint, FaceID, etc).
Software safety and Infrastructure
Dedicated Servers
Delivered by DigitalPA dedicated Servers: Maximum data security and protection at the highest levels, guaranteed by the DigitalPA ISO 27001/2014 certification and by the certified server farm infrastructure ISO 27001/2017;
OWASP tested
Testing on the system vulnerability and safety through best practices;
CSRF Prevention
All requests managed by the platform are protected by CSRF token;
IP blocking
Limited access to the client’s IP addresses list. The platform can then be accessed from the internet or exclusively from the intranet;
SSL Certificate
Whistleblowing is only accessible through HTTPS (Secure Sockets Layers);
Integrated Firewall
Hardware and Software: each platform has an integrated firewall with very strict rules, which limit access and actions to the software. The firewalls integrate and enhance security;
User input validations
The platform is built with a user validation-based approach. Through extremely strict rules the user input is verified both at a client/server level;
IP / SSL Certificate
IP and SSL certificate: dedicated for each customer;
Legality Whistleblowing software is compliant with international directives and the EU GDPR Regulation
Using Legality Whistleblowing, your organization will be able to achieve the ISO 37001, ISO 37002, and ISO 37301 certifications, relating to Anti-Bribery, Whistleblowing, and Compliance management systems respectively.
ISO 37001
Anti-Bribery
ISO 37002
Whistleblowing management
ISO 37301
Compliance management
Oracle Cloud Infrastructure (OCI)
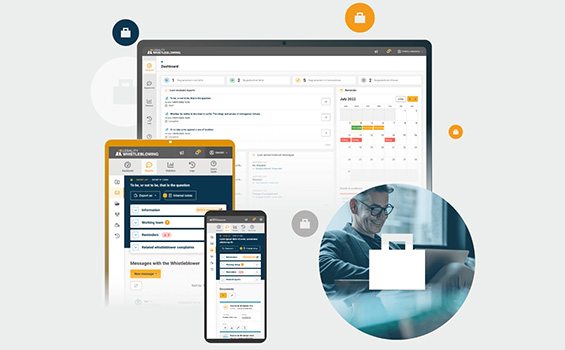
Legality Whistleblowing is a Web Based Software in Oracle infrastructure – a Cloud Provider able to guarantee high performance, data security, and business continuity.
Contact us
Discover our advanced software solution for wrongdoing reporting today by scheduling a demo.
